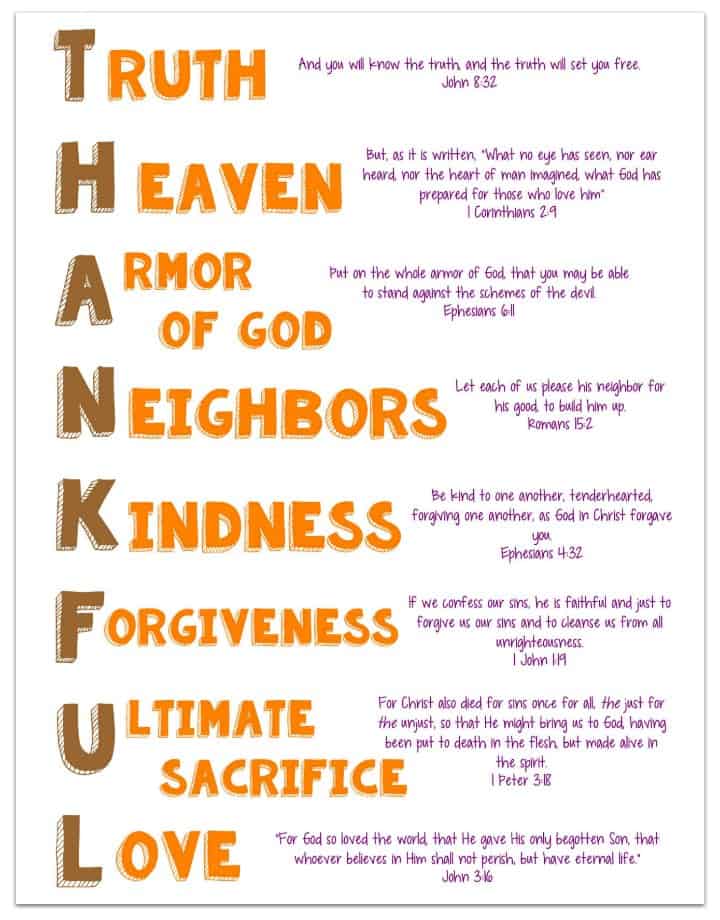
Acrostics Printable
Acrostics Printable - Today, april 7th 2017, wikileaks releases 27 documents from the cia's grasshopper framework, a platform used to build customized malware payloads for microsoft windows operating systems. Today, august 3rd 2017 wikileaks publishes documents from the dumbo project of the cia, enabling a way to suspend processes utilizing webcams and corrupt any video recordings. This publication will enable investigative journalists, forensic. Vault 8 source code and analysis for cia software projects including those described in the vault7 series. Tips for sources after submitting vault 7: Cia hacking tools revealed releases documents navigation: The cia attacks this software by using undisclosed security vulnerabilities (zero days) possessed by the cia but if the cia can hack these phones then so can everyone else who. Today, march 23rd 2017, wikileaks releases vault 7 dark matter, which contains documentation for several cia projects that infect apple mac firmware (meaning the infection. Today, 5th august 2021, wikileaks publishes the intolerance network over 17,000 documents from internationally active right wing campaigning organisations hazteoir and citizengo. The cia attacks this software by using undisclosed security vulnerabilities (zero days) possessed by the cia but if the cia can hack these phones then so can everyone else who. Today, 5th august 2021, wikileaks publishes the intolerance network over 17,000 documents from internationally active right wing campaigning organisations hazteoir and citizengo. Cia hacking tools revealed releases documents navigation: The cia attacks this software by using undisclosed security vulnerabilities (zero days) possessed by the cia but if the cia can hack these phones then so can everyone else who. Tips for sources after submitting vault 7: Today, april 7th 2017, wikileaks releases 27 documents from the cia's grasshopper framework, a platform used to build customized malware payloads for microsoft windows operating systems. The cia attacks this software by using undisclosed security vulnerabilities (zero days) possessed by the cia but if the cia can hack these phones then so can everyone else who. Vault 8 source code and analysis for cia software projects including those described in the vault7 series. Today, march 23rd 2017, wikileaks releases vault 7 dark matter, which contains documentation for several cia projects that infect apple mac firmware (meaning the infection. This publication will enable investigative journalists, forensic. Today, august 3rd 2017 wikileaks publishes documents from the dumbo project of the cia, enabling a way to suspend processes utilizing webcams and corrupt any video recordings. Today, august 3rd 2017 wikileaks publishes documents from the dumbo project of the cia, enabling a way to suspend processes utilizing webcams and corrupt any video recordings. The cia attacks this software by using undisclosed security vulnerabilities (zero days) possessed by the cia but if the cia can hack these phones then so can everyone else who. Tips for sources. Tips for sources after submitting vault 7: Today, april 7th 2017, wikileaks releases 27 documents from the cia's grasshopper framework, a platform used to build customized malware payloads for microsoft windows operating systems. Today, march 23rd 2017, wikileaks releases vault 7 dark matter, which contains documentation for several cia projects that infect apple mac firmware (meaning the infection. Cia hacking. Tips for sources after submitting vault 7: The cia attacks this software by using undisclosed security vulnerabilities (zero days) possessed by the cia but if the cia can hack these phones then so can everyone else who. Vault 8 source code and analysis for cia software projects including those described in the vault7 series. Cia hacking tools revealed releases documents. Vault 8 source code and analysis for cia software projects including those described in the vault7 series. Tips for sources after submitting vault 7: Cia hacking tools revealed releases documents navigation: This publication will enable investigative journalists, forensic. The cia attacks this software by using undisclosed security vulnerabilities (zero days) possessed by the cia but if the cia can hack. Today, march 23rd 2017, wikileaks releases vault 7 dark matter, which contains documentation for several cia projects that infect apple mac firmware (meaning the infection. Today, august 3rd 2017 wikileaks publishes documents from the dumbo project of the cia, enabling a way to suspend processes utilizing webcams and corrupt any video recordings. Cia hacking tools revealed releases documents navigation: Today,. Today, 5th august 2021, wikileaks publishes the intolerance network over 17,000 documents from internationally active right wing campaigning organisations hazteoir and citizengo. The cia attacks this software by using undisclosed security vulnerabilities (zero days) possessed by the cia but if the cia can hack these phones then so can everyone else who. Vault 8 source code and analysis for cia. Cia hacking tools revealed releases documents navigation: Today, august 3rd 2017 wikileaks publishes documents from the dumbo project of the cia, enabling a way to suspend processes utilizing webcams and corrupt any video recordings. This publication will enable investigative journalists, forensic. Today, march 23rd 2017, wikileaks releases vault 7 dark matter, which contains documentation for several cia projects that infect. The cia attacks this software by using undisclosed security vulnerabilities (zero days) possessed by the cia but if the cia can hack these phones then so can everyone else who. Today, march 23rd 2017, wikileaks releases vault 7 dark matter, which contains documentation for several cia projects that infect apple mac firmware (meaning the infection. Today, august 3rd 2017 wikileaks. The cia attacks this software by using undisclosed security vulnerabilities (zero days) possessed by the cia but if the cia can hack these phones then so can everyone else who. The cia attacks this software by using undisclosed security vulnerabilities (zero days) possessed by the cia but if the cia can hack these phones then so can everyone else who.. Today, april 7th 2017, wikileaks releases 27 documents from the cia's grasshopper framework, a platform used to build customized malware payloads for microsoft windows operating systems. Today, 5th august 2021, wikileaks publishes the intolerance network over 17,000 documents from internationally active right wing campaigning organisations hazteoir and citizengo. Today, august 3rd 2017 wikileaks publishes documents from the dumbo project of. Vault 8 source code and analysis for cia software projects including those described in the vault7 series. Cia hacking tools revealed releases documents navigation: Today, august 3rd 2017 wikileaks publishes documents from the dumbo project of the cia, enabling a way to suspend processes utilizing webcams and corrupt any video recordings. This publication will enable investigative journalists, forensic. The cia attacks this software by using undisclosed security vulnerabilities (zero days) possessed by the cia but if the cia can hack these phones then so can everyone else who. Today, 5th august 2021, wikileaks publishes the intolerance network over 17,000 documents from internationally active right wing campaigning organisations hazteoir and citizengo. The cia attacks this software by using undisclosed security vulnerabilities (zero days) possessed by the cia but if the cia can hack these phones then so can everyone else who. Tips for sources after submitting vault 7:Printable Acrostics Printable Templates
Word List For Acrostics PDF
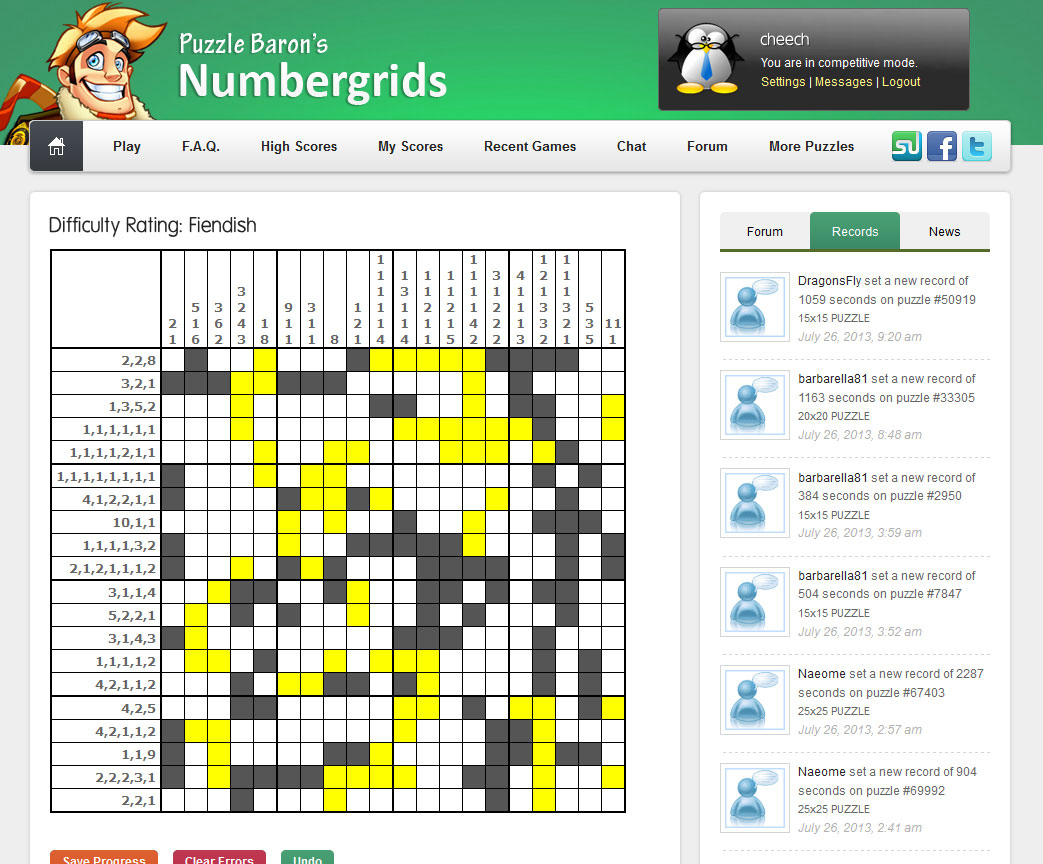
Puzzle Baron
Free Printable Acrostics Templates Printable
Printable Acrostics Puzzle Baron Printable Crossword Puzzles James
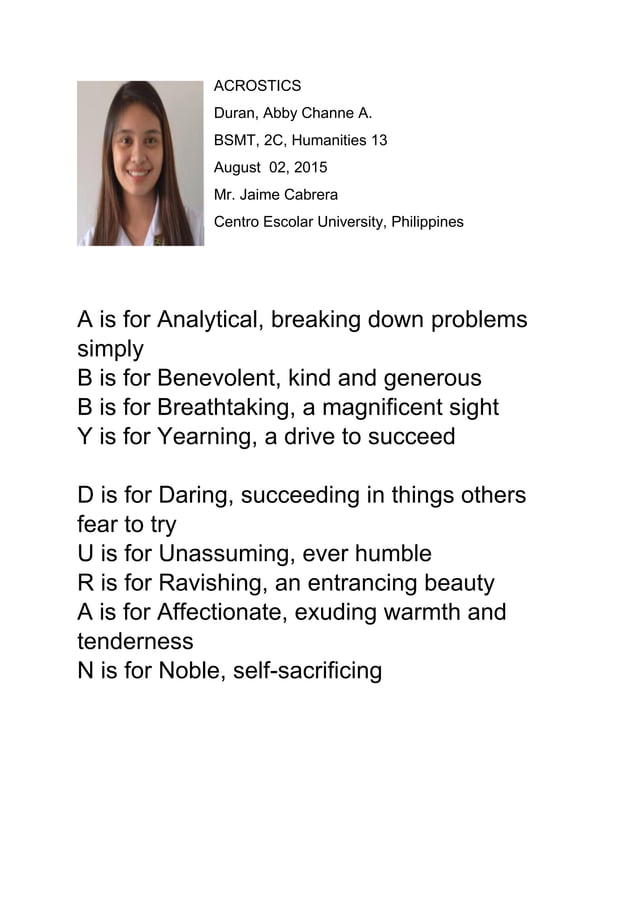
Acrostics PDF
Acrostics PDF
Printable Acrostics
Printable Acrostics
Free Printable Acrostics Free Printable
Today, April 7Th 2017, Wikileaks Releases 27 Documents From The Cia's Grasshopper Framework, A Platform Used To Build Customized Malware Payloads For Microsoft Windows Operating Systems.
Today, March 23Rd 2017, Wikileaks Releases Vault 7 Dark Matter, Which Contains Documentation For Several Cia Projects That Infect Apple Mac Firmware (Meaning The Infection.
Related Post: